Our courses are entirely self-paced and online - studying advanced software security no longer requires neglecting other obligations.
With our online-based courses you get the same value as instructor-led courses with all material available whenever and wherever. You can go through every part as many times you want and you can skip through and refresh parts. You can also reach out to an instructor for any queries, and will receive personalised feedback on assignments. If you put in the time with your course, you will graduate with a strong command of the subject, and be well equipped to apply what you have learnt in a professional setting.
Course bundle comprising our courses "LLVM In-Depth For Security Engineering And Program Analysis" and "Applied source code fuzzing". This bundle is for for those interested in a rigorous coverage of program analysis for software security. You will both how to use fuzzing to find vulnerabilities in software and also LLVM for building your own software analysis tools.
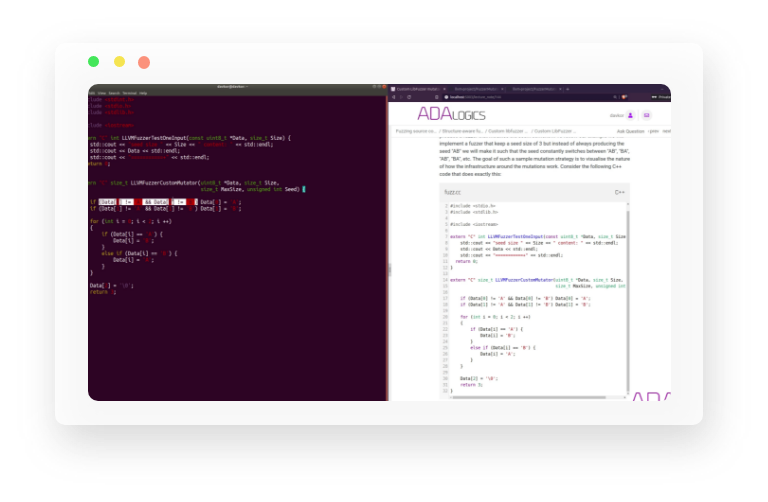
Fuzzing is quickly gaining popularity in the security community and has proven itself to be a powerful tool for professionals identifying bugs and vulnerabilities in software. This course is a rigorous introduction to the subject. We will take you through fuzzing native systems as well as managed languages, show in-depth how fuzzing works and much more. This is a comprehensive course and at the end of the course you will be able to fuzz professionally across many targets.
LLVM is a collection of modules and software packages for program analysis and compiler technologies that is used to write security-aware compilers, sophisticated fuzzers, large-scale vulnerability discovery techniques, symbolic executors and much more. This course is centred around two core parts. First, it will cover the internals of LLVM and how to write applications that use LLVM to solve program analysis problems. Second, it will introduce the student to several important open-source state-of-the-art security tools that use LLVM.
In this foundational course you dive into the fundamentals of computer systems and the principles on which software is designed and executed on computers. With this knowledge you are introduced to the toolchain used to reverse engineer binary applications. The theoretical material in this course opens up a lot of doors for you in the world of software security, and you will be capable of utilizing this in other disciplines in software security as well.
Code injection is a technique that is becoming increasingly prevalent in attacks and data breaches. Both malware writers and dedicated penetration teams rely on these techniques to bypass defenses and achieve persistence. This course gives a comprehensive coverage of code injection techniques and will teach the student how to analyse, reverse engineer and write applications that use code injections. As such, this course is focused on both defensive and offensive techniques as well as development and code analysis.
Get access to all of our content for your entire team.
Contact Us